Product
Safari leaks private data, Ghostery has a quick fix
On January 14th, FingerprintJS disclosed a critical vulnerability in WebKit that affects both Safari on Desktop and all mobile browsers on iOS and iPadOS.
The bug that they discovered is related to a security concept that prevents trackers from reading information from other sites (“same-origin policy”). In this case, data stored by websites via an API called IndexedDB is available to any script running in the browser.
Why is it critical?
- It leaks parts of your browsing history (e.g. whether you visited YouTube, Instagram or Twitter).
- If you are logged in with your Google account, it allows trackers to read your Google User ID, thus revealing your identity.
FingerprintJS first reported the issue to Apple on November 28th 2021, but only after its disclosure in January 2022 it received public attention.
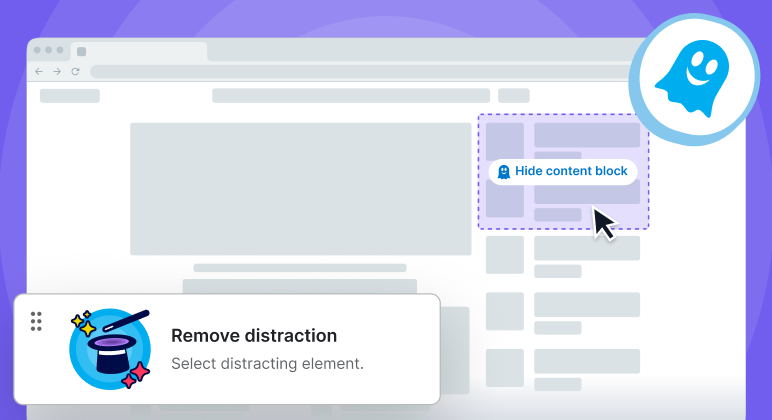
Today, we released Ghostery 9.2.0 for Safari. It ships with the first mitigation of the attack to protect Safari users.
We hope that Apple will release a fundamental improvement soon with a new release of their desktop browser and new version of iOS and iPadOS - but that takes time.
For this vulnerability, we were able to provide a mitigation in the Ghostery extension. And being an extension allows us to roll it out independently of operating system updates. We believe it is our role to support the browser ecosystem in events like this.
What should you do?
Get a fix, download Ghostery.
Learn more: FingerpringJS demonstrates the issue on their website safarileaks.com and covers it in details in their blog post.